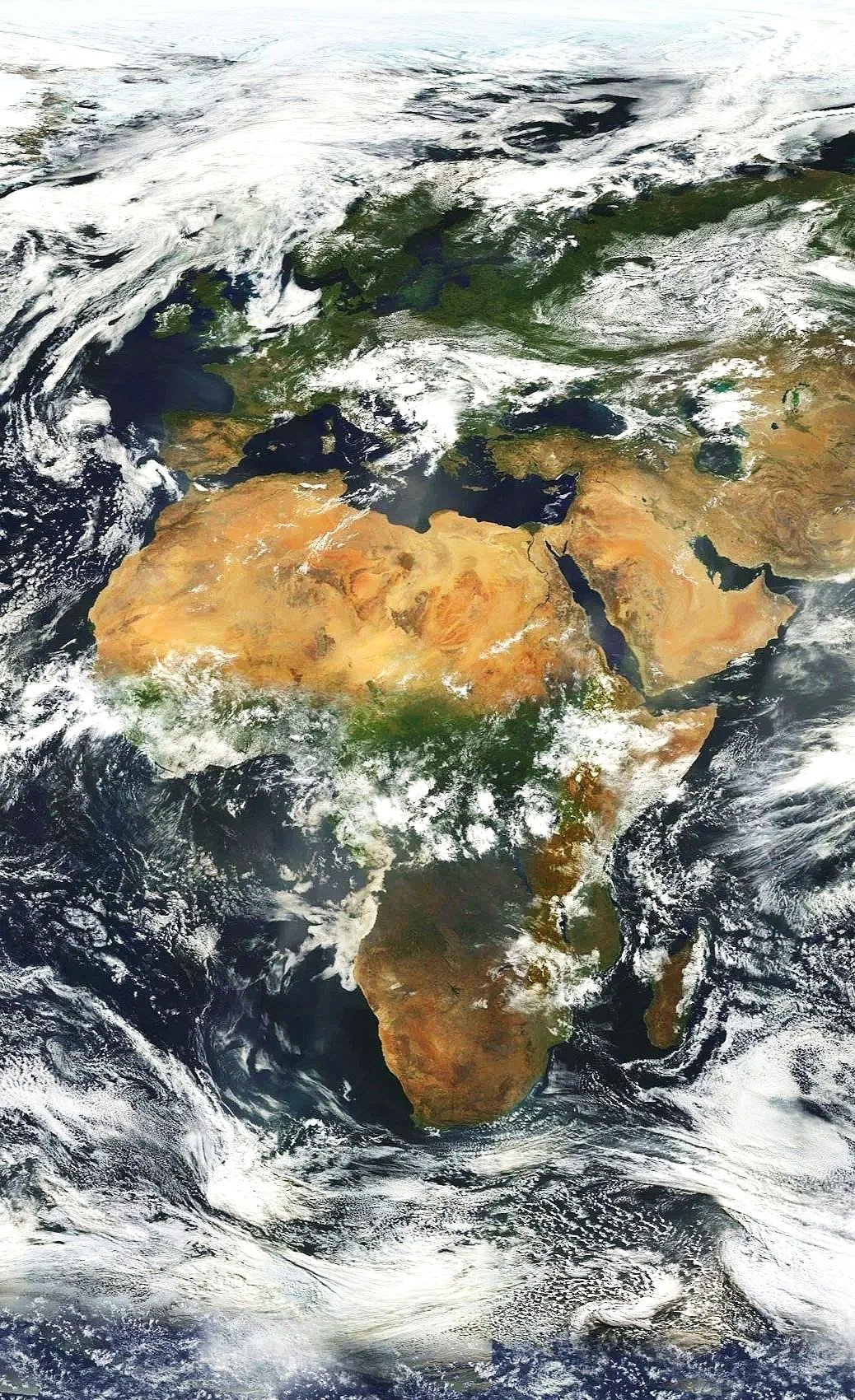
Strategic Security & Risk Advisory Across the Middle East & Africa…
30 years. Middle East & Africa. Oil & Gas, Telecoms, Mining & Minerals, critical infrastructure.
When something goes wrong in this part of the world, the margin for error is already gone.
Absolute Risk Management provides security risk and design services across the Middle East and Africa — for organisations operating in environments where the stakes are real, the terrain is complex, and the consequences of getting it wrong are immediate.
This is not a firm built on templates, frameworks, or desk-based analysis. It was built on thirty years of working in the same environments as our clients as a former British Army officer, former government intelligence professional, and senior security leader inside some of the world's largest organisations..
That experience is the basis of everything we do.
You already know what a good assessment looks like. Finding someone who can actually deliver one is the problem. If you're a security director or risk manager operating in MEA, you've seen what the standard firms produce. Polished frameworks. Comprehensive-looking reports. Risk registers that bear little resemblance to what's actually happening on the ground.
In this region, that gap isn't just frustrating. It's dangerous.
The Middle East and Africa are environments where the situation changes fast, where cultural nuance is everything, and where a security plan built on outdated intelligence or desk-based assumptions will fail, not theoretically, but operationally, when it matters.
Absolute Risk Management was built by someone on your side of the table, demanding real intelligence, rejecting substandard assessments, and taking personal responsibility for the safety of people in genuinely hostile environments.
Our Service and Approach
Across all services, the method remains consistent. The first task is to establish the real position, not the assumed one. The second is to assess the risk properly. The third is to define what is actually required. The fourth is to shape that into a credible security design direction. This is a disciplined process, but a practical one. Security has to function inside live operations, difficult environments, tight budgets, and ageing infrastructure. The work has to reflect that, not ignore it.
That is the basis on which Absolute Risk Management operates:
A security survey establishes the true physical and operational condition of a site, facility, or critical asset by examining how existing measures perform in practice and where weaknesses remain. Whether conducted remotely from available drawings and imagery or through a full on-site inspection, the survey reviews perimeter security, access and egress, lighting, surveillance, guarding, patrol functions, and supporting infrastructure to provide a clear picture of current standards and what requires improvement.
Absolute Risk Management provides hotel security assessments to help organisations make sound accommodation decisions for business travellers operating in higher-risk or unfamiliar environments. The service examines how a hotel functions in practice, including access control, lobby and lift security, guard capability, CCTV coverage, emergency arrangements, and the separation of public, guest, and service areas, giving corporate security managers a clear and defensible basis for approval decisions.
Security Risk Assessments are used to identify what must be protected, understand the threats that could affect it, assess the vulnerabilities that could be exploited, and determine the likely consequences of a successful incident. The result is a practical, risk-based assessment that considers people, infrastructure, operations, systems, and governance, allowing clients to prioritise proportionate mitigation measures that support informed decisions rather than theoretical compliance.
Once the risk picture is understood, Absolute Risk Management defines the system and operational requirements needed to protect an asset properly. This service sets out, in clear terms, the technical measures, manpower, procedures, monitoring, response arrangements, and stakeholder considerations required before capital is committed, ensuring the client understands exactly what is needed and why before progressing into detailed design or procurement.
Absolute Risk Management develops high-level conceptual security design proposals based on survey findings, risk assessments, and defined operational requirements. The purpose is to present a structured, risk-based design direction for the client and relevant stakeholders, covering elements such as perimeter protection, checkpoints, access control, surveillance, intrusion detection, guard infrastructure, and control room oversight, without moving prematurely into final engineering design or procurement detail.
What You Will Receive
At the end of any engagement, the client has something tangible: a clear picture of the current security position, a risk-based assessment they can stand behind, defined requirements that can be taken into design and procurement, and where required, a conceptual design direction ready for further development.
These are not theoretical outputs. They are tools. Built to be used.
"Most consultancies are great at identifying gaps. Fewer are good at providing a budget conscious and technically viable roadmap, one that actually supports the conversation with finance."
Regional Security Manager, Global Oil & Gas Company
This is exactly the gap ARM is built to close. Every output we produce is sized to what the client can actually implement and structured to support the internal conversation, not just satisfy the assessment requirement. A security recommendation that cannot survive a conversation with the Finance Director is not a recommendation. It is a liability.
"They have a set menu of what they do and what they sell. I don't have the same menu of needs. A good one will flex to deliver the need not flex the need to match their deliverables."
Senior Security Director, Global Infrastructure Company
We don't arrive with a fixed menu. We arrive with a question: what does this specific site, in this specific environment, actually need? The services ARM offers reflect the most common requirements but the scope, depth, and sequencing of any engagement is built around the client's situation. Not the other way around.

